Identity Theft Prevention Techniques
Identity theft prevention blends awareness with disciplined routines. Strong, unique passwords and multi-factor authentication form the first line of defense, complemented by regular software updates and device hygiene. Practice selective sharing and verify requests through official channels to resist social engineering. Daily monitoring and data minimization reduce risk, while robust access controls and encryption preserve security. Ongoing threat awareness and rapid response plans are essential, yet gaps remain that demand careful attention as circumstances evolve.
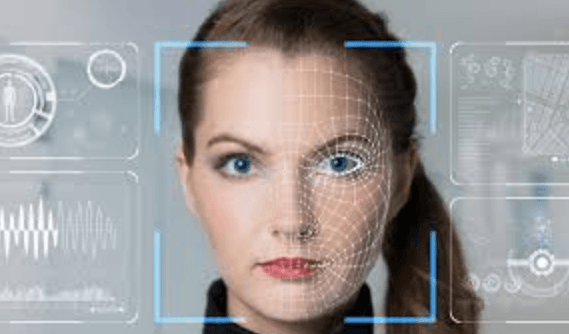
What Is Identity Theft and Why It Happens
Identity theft is the unauthorized use of another person’s personal information to commit fraud or other crimes.
The phenomenon stems from data exposure, social engineering, and weak verification.
By analyzing vectors, it illuminates why it happens and where privacy pitfalls lie.
Awareness reveals potential financial risk, guiding proactive safeguards and disciplined monitoring to preserve autonomy and freedom from exploitation.
Build a Digital Defense: Daily Habits to Prevent Fraud
A disciplined daily routine forms the backbone of effective fraud prevention, translating high-level safeguards into concrete, repeatable actions. The analysis identifies simple, reproducible practices that reinforce privacy hygiene and credential safety, reducing exposure to theft. Routine tasks include password hygiene, device updates, selective sharing, and secure authentication. A disciplined cadence enables proactive resilience, preserving autonomy while restricting attack surfaces.
Proactive Monitoring: How to Detect and Respond Fast
Proactive monitoring integrates real-time data collection, anomaly detection, and rapid response to identify and mitigate fraud as it unfolds. The approach emphasizes structured surveillance, cross-channel alerts, and auditable actions, enabling swift containment. Analysts evaluate patterns, prioritize threats, and implement containment without delay. This framework promotes proactive monitoring ideas and quick response strategies, preserving autonomy while reducing exposure to evolving risks.
See also: shortcutmagazine
Smart Data Management: Protecting Personal Information Long-Term
Effective long-term protection of personal data requires a structured approach that prioritizes data minimization, robust access controls, and durable encryption.
In Smart Data Management, organizations implement data stewardship frameworks and privacy governance to ensure persistent data lifecycle discipline, minimize exposure, and sustain resilience.
The approach emphasizes clear roles, auditable trails, and continuous improvement to preserve user autonomy and systemic integrity.
Frequently Asked Questions
How Can I Recover a Stolen Identity Quickly?
To recover a stolen identity rapidly, one should initiate fraud alerts and a credit freeze, then monitor reports and dispute inaccuracies; implement rapid steps, document all communications, secure accounts, and pursue legal remedies while preserving personal sovereignty and autonomy.
What Are Telltale Signs of a Data Breach?
A data breach indicators include suspicious login alerts and anomalous account activity, prompting immediate verification of account details, credit reports, and security settings; proactive monitoring and rapid response minimize damage and empower individuals to reclaim control with informed vigilance.
Which Credit Bureau Should I Place Fraud Alerts With?
The appropriate credit bureau for placing fraud alerts depends on jurisdiction; generally, one should contact all major credit bureaus to ensure comprehensive coverage. Fraud alerts should be initiated promptly, and periodic checks maintained to preserve financial freedom.
How Do I Securely Dispose of Old Documents?
A careful archivist, like a river cutting through rock, advises secure shredding and proper document disposal to prevent leakage. The approach remains analytical, proactive, and precise, empowering individuals seeking freedom through disciplined, permanent destruction of sensitive records.
Can I Freeze My Credit Across All Lenders?
Yes, one can freeze credit across all lenders, ensuring broad protection; additionally, place fraud alerts with bureaus to prolong scrutiny. The approach is analytical and proactive, offering freedom through precise controls and proactive monitoring.
Conclusion
In sum, identity theft prevention rests on disciplined routines and vigilant systems. The outlined practices—strong, unique passwords, multi-factor authentication, timely software updates, and minimized data exposure—form a cohesive defense rather than isolated tactics. By coupling daily monitoring with proactive threat detection and rapid response protocols, individuals can swiftly contain incidents and preserve financial integrity. Like a well-tortured lock with an adaptive shield, a layered, auditable approach compounds protection while reducing vulnerability to evolving scams.