Identity Verification Technologies
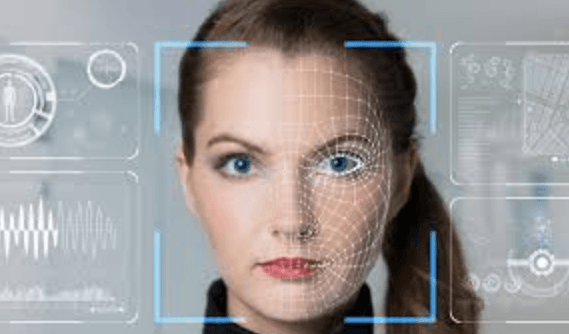
Identity verification technologies assemble multiple signals—user data, verifiable credentials, biometrics, liveness checks, and device fingerprints—into a confidence score guiding risk-based authentication. They balance privacy-by-design, data minimization, and governance with auditability. Cross-border feasibility, consent, and portability shape practical deployment. The framework supports adaptable architectures and proportionate safeguards, aiming for user autonomy without compromising fraud protection and regulatory compliance. Questions remain about trade-offs, implementation complexity, and ongoing governance as new threats emerge.
How Identity Verification Works Today
Identity verification today relies on a layered approach that combines user-provided information with verifiable credentials and biometric data. This framework analyzes signals like liveness detection, device fingerprinting, and cross-referenced records to form a confidence score. Fraud indicators are flagged automatically, prompting additional checks or risk-based authentication. The method remains transparent, adaptable, and oriented toward user autonomy within secure boundaries.
Choosing the Right Verification Methods
Selecting an appropriate mix of verification methods requires a structured assessment of risk, user context, and operational constraints. The analysis identifies suitable factors, balancing privacy norms, consent mechanisms, and data portability. It evaluates cross border verification feasibility, implementing liveness checks and device fingerprinting where appropriate, while maintaining audit trails. Decisions are documented, repeatable, and aligned with governance, security, and user empowerment goals.
Balancing Privacy, Security, and Convenience
The assessment delineates privacy tradeoffs inherent in verification workflows, weighing data minimization against accuracy.
It acknowledges user consent as a critical control point, ensuring transparency and choice.
Decisions favor adaptable architectures, measurable safeguards, and ongoing governance without compromising fundamental freedoms.
Evaluating Risks and Compliance Impacts
Emerging from the discussion of privacy, security, and convenience, this section assesses the risk landscape and regulatory implications of identity verification technologies.
The analysis identifies privacy risk drivers, including data collection breadth, transform practices, and cross-border flows, and emphasizes governance through data minimization.
Compliance considerations address risk-based oversight, auditability, and proportionate safeguards aligned with emerging standards.
Frequently Asked Questions
How Long Does Identity Verification Data Remain Stored?
Data retention varies by jurisdiction and policy, but generally relatives of compliance timelines govern storage durations; organizations should balance accuracy with privacy implications, implement minimization, and establish deletion schedules to minimize risk and meet data retention and privacy regulation expectations.
Can Verification Results Be Appealed or Corrected?
Silhouettes of scales shimmer; verification results may be appealed or corrected through a defined appeal process and data correction mechanisms. The analysis is precise and methodical, ensuring transparency for individuals who seek freedom within regulated data practices.
What Are Common False Negative Causes in Biometrics?
False negatives in biometrics arise from biometric error sources such as sensor noise, poor sample quality, and alignment issues; environmental factors and user condition variability exacerbate failures, while algorithmic thresholds and population diversity also influence false negative rates.
Do Verification Apps Work Offline or Require Internet?
Offline functionality varies by app; some work without internet, others require periodic data sync. The data sync frequency influences recent verification accuracy and risk exposure, while offline modes emphasize continuity and user autonomy amid intermittent connectivity.
See also: Identity Theft Prevention Techniques
How Do Cultural Biases Affect Verification Accuracy?
Cultural bias can skew verification accuracy; cross-cultural data reduces variance by diversifying datasets. Data collection must account for biometric demographics to avoid systematic error, ensuring fair performance across populations while preserving methodological rigor and user autonomy.
Conclusion
Identity verification technologies integrate layered signals—user data, verifiable credentials, biometrics, liveness, and device fingerprints—into a confidence score that guides risk-based authentication. The approach emphasizes privacy-by-design, data minimization, governance, and auditability. Cross-border feasibility and consent mechanisms shape portability and user autonomy. A methodical evaluation shows proportional safeguards, adaptable architectures, and ongoing oversight as essential. Coincidence arises when privacy, security, and usability unexpectedly align, yielding robust protection without friction—yet only through disciplined governance and continuous risk monitoring.